Your website keeps working. Whether you think about it or not.
A website requires ongoing attention: plugin updates that break things if not tested, security vulnerabilities that need patching, backups that need to actually run, and performance that degrades without maintenance. The VIP Protection Plan handles all of this without the client needing to think about it.
Most business websites are built, launched, and then ignored until something goes wrong. The consequences range from minor — a broken contact form nobody notices for weeks — to serious: a hacked site, a Google penalty for malware, or a lost e-commerce order trail that no one can reconstruct.
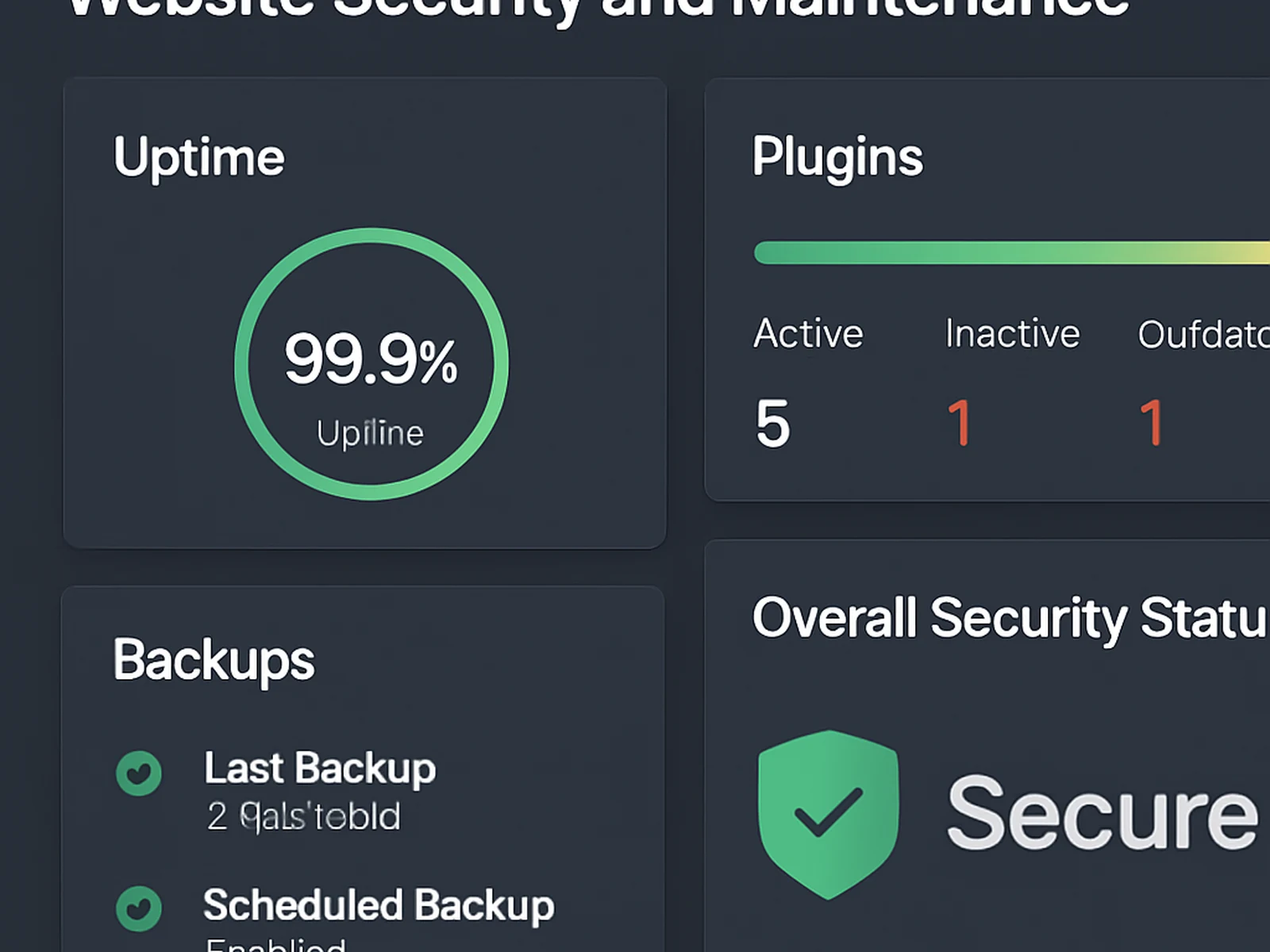
The VIP Protection Plan operates on a monthly cycle. Plugin, theme, and core updates are applied to a staging environment, compatibility-tested, then pushed to production. This staging step is important — a plugin update that breaks a contact form or causes a layout regression is identified before it affects visitors, not after.
Security scans run weekly. Backups run daily to off-site storage with a tested restoration process. Monthly performance checks compare against the baseline established at launch.
The plan includes a monthly content update allowance of two hours — enough for text changes, image swaps, or a new team member page. Most care plan clients use this allowance consistently. It keeps the site current without requiring the client to maintain a developer relationship for minor changes.
For websites we did not build, we run a two-week onboarding audit before starting the plan: assessing the existing code quality, fixing immediate issues, and establishing the maintenance baseline. The audit is included in the plan price.
The plan is billed annually. For businesses on the plan for two or more consecutive years, the renewal rate does not increase.
In practice
A professional services firm in Florence on the VIP Protection Plan avoided a major ransomware incident when our weekly scan flagged a compromised plugin before the exploit was triggered. The fix took 90 minutes. The alternative — a hacked site, data breach notification obligations, and reputational damage — would have been considerably more expensive.
An e-commerce client on the plan received an alert about a critical WooCommerce vulnerability twelve hours after it was publicly disclosed. The patch was applied to staging, tested, and pushed to production before any exploit attempt was made.
Questions about this service
Start
VIP Protection Plan.
Tell us about your project. We reply within one business day with an honest assessment and a clear proposal.